Top 5 considerations on the effects of COVID-19 in securing your business

By
NEED AUTHOR
on
May 27, 2020 4:37:50 PM
Tags: Security, Large Business and Government, Data Protection, COVID-19, Covid-19 Preparations
As corporations are forced to rapidly adapt to a new environment in order to remain viable, securing data and infrastructure must be taken into consideration when changes are made. Considerations such as:
- Does your VPN have the latest updates and patches?
- Do you have multi-factor authentication implemented to help protect against credential theft?
- How do you protect remote workers when your assets sit on untrusted networks?
- Do you understand your risk tolerance including the controls and processes around them?
- How do you adjust your risk management practices in the age of global pandemics?
When the reactive stage has finally calmed down, it will be time to examine your security posture from beginning to end.
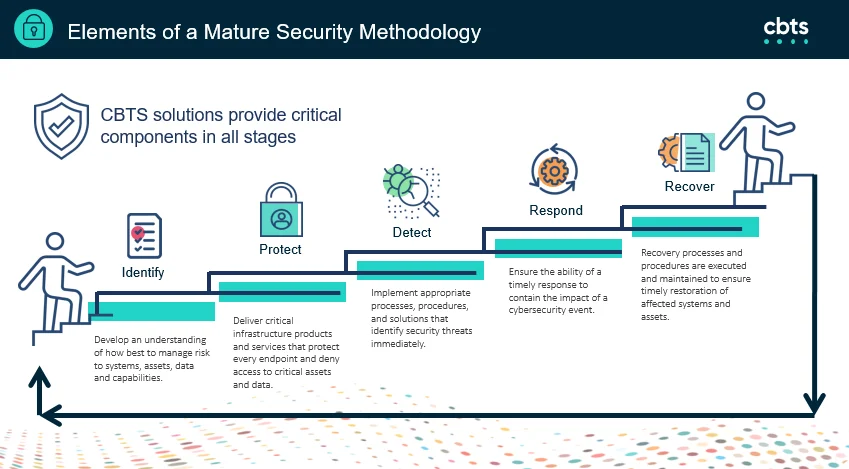
- Identify - Develop an understanding of how best to manage risk to systems, assets, data and capabilities
- Protect - Deliver critical infrastructure products and services that protect every endpoint and deny access to critical assets and data.
- Detect - Implement appropriate processes, procedures and solutions that identify security threats immediately.
- Respond - Ensure the ability of a timely response to contain the impact of a cybersecurity event.
- Recover - Recover processes and procedures are executed and maintained to ensure timely restoration of affected systems and assets.
If you are in need of immediate help or advice on what improvements are required during this crisis, the CBTS Security team is here to assist you in any way. Learn More
.png?width=350&height=124&name=HAWN_TELCOM_LOGO_two-color-RGB%20(1).png)