The beauty of having different climates around the world is that there is always somewhere we can travel for…
Filters:
Security Articles
When it comes to cybersecurity, your best offense is a fiber-fortified defense. Not only does fiber internet…
|
Secure Network from Hawaiian Telcom empowers your business with unmatched protection, superior network… |
If you’re a small or medium-sized business (SMB) owner, you know you have to balance the need to increase…
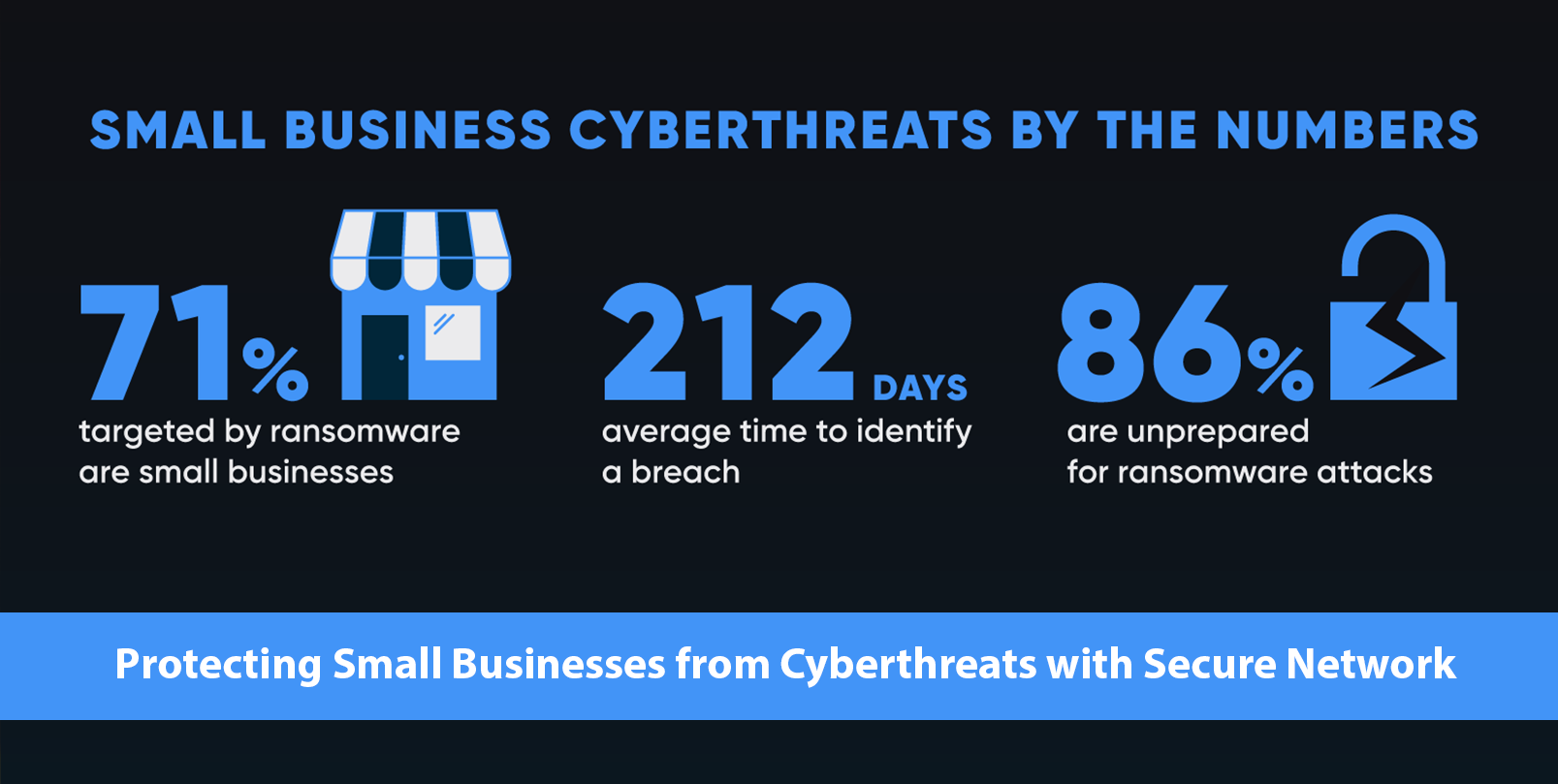
Ransomware attacks, where malicious software encrypts a victim's data and demands a ransom for decryption,…
|
Hawaiian Telcomis pleased to announce the launch of Secure Network, an enterprise-grade network… |
71% of ransomware attacks impact small businesses. Aside from the devastating financial implications, a…
Effective budgeting is crucial for the success of any organization. The constantly changing state of…
The “Internet of Things” has changed the way many of us live both at home and in our businesses. The ability…
We had a great time at BSides Hawaii Info-Sec Conference held at the Prince Waikiki on May 24, 2023.…